Higher education has a data problem, and it runs deeper than recent headlines suggest.
Colleges and universities have quietly become one of the most targeted groups in cybersecurity. Across 2025, education saw a 75% surge in weekly cyberattacks. Each breach costs an institution over $3 million on average, even before accounting for downtime, reputational fallout, or the years of harm that follow students whose data ends up for sale.
But all the statistics tend to miss a critical element: the data stolen in one attack often becomes the tool used in the next one. Student and faculty identity verification procedures must adapt, or the breaches will keep coming.
Student Information Keeps Getting Stolen & Reused
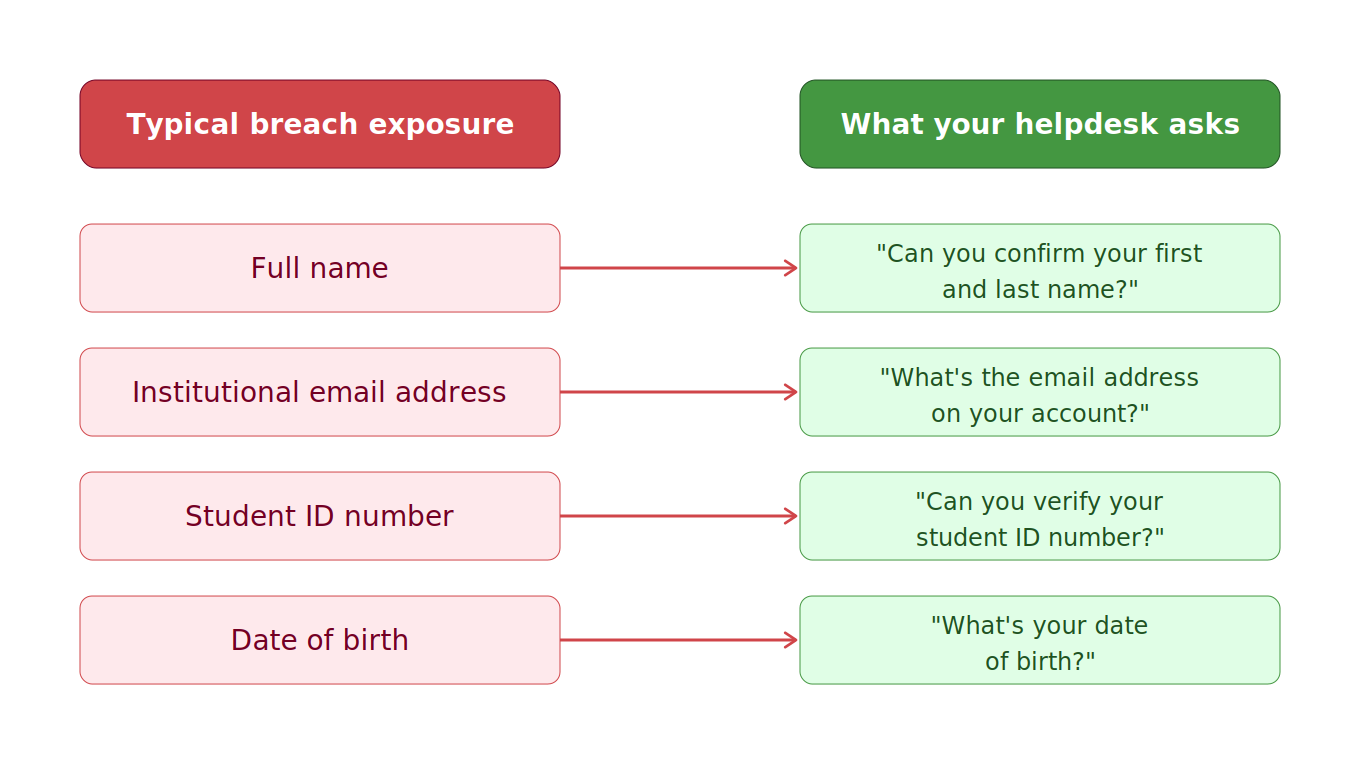
The data exposed in higher ed breaches follows a recognizable pattern: Names, email addresses, student ID numbers, sometimes dates of birth, sometimes Social Security numbers, sometimes more detailed data like financial records or even private messages.
The 2023 MOVEit breach is a useful reference point. A single vulnerability in a widely-used file transfer tool hit more than 800 educational organizations and exposed nearly 1.7 million student and staff records. The data involved was the kind that populates any university system: identifiers, contact details, enrollment records. Unremarkable until it isn't.
More recently, a breach of a major ed-tech platform used by tens of millions of students across thousands of institutions exposed a similar data set: names, email addresses, student ID numbers, and messages between users. The attacker got in through a compromised support credential. It wasn't a sophisticated zero-day; it was an identity problem.
The through-line across incidents like these is consistent. Attackers aren't collecting this data as an end goal. They're collecting it because of what it lets them do next.
The University Helpdesk Problem Nobody Talks About
Picture what happens after student records leak.
An attacker now has a file: first name, last name, student ID number, institutional email address. At many universities, that's sufficient to successfully impersonate a student, because those are often the exact fields a university IT helpdesk will ask for when a student calls to reset a password, recover an account, or get access to university resources.
"Can you verify your student ID number?"
It was a reasonable question before that information was circulating on the dark web. Today, knowledge-based verification of this kind isn't verification. It's a formality that hands attackers everything they need to impersonate a legitimate student, bypass account security, and access email, financial aid portals, grade records, or anything else tied to that account.
This is social engineering at its most basic. No phishing email, no malware, no technical skill required. The attacker calls, recites the data from the breach, and the helpdesk does exactly what it was trained to do.
The fault isn't with helpdesk staff. They're following the process they were given. The process, though, was built for a world where student ID numbers were private. That world is gone.

Breached Data Has a Long Shelf Life
The part that often gets lost in breach coverage is that the data doesn’t expire. Comparitech research found that education companies take an average of 6.3 months to report a breach. By the time students receive a notification — if they receive one at all — their information has likely been packaged and sold. Unlike a compromised password, a student ID number doesn't get reset. It follows a student for years, often for life as an alumni identifier.
Institutions aren't just managing the risk of today's breach. They're carrying the cumulative exposure of every incident that has touched their student population. A student who enrolled in 2019 may have had their information surface in several separate incidents since then. Each one adds another layer of data available to anyone who wants to impersonate them.
For IT and security teams, this reframes the right question to ask at the helpdesk. Not "does this person know their student ID?" but "is this actually the person they claim to be?" Those are different questions. Only one of them is worth building a verification process around.
Student & Faculty Onboarding Is Just as Exposed
The helpdesk is the most obvious vulnerability. It isn't the only one.
Student onboarding is another point of real exposure. At many institutions, this process still relies on static identifiers: admission ID, date of birth, last four of a Social Security number. Depending on which systems have been breached over the years, that information may already be in circulation before the student ever logs in for the first time.
Account takeover at onboarding is particularly consequential because it happens at the start of a student's relationship with the institution. An attacker who claims an account at that point can intercept financial aid disbursements and establish control before the legitimate student realizes what's happened. Recovery is painful for everyone involved.
The risk is compounded for institutions that have expanded online programs. When a student has never set foot on campus, the digital identity is the identity. If it was compromised at creation, everything built on top of it is exposed.
How Student & Faculty Verification Must Evolve
The institutions getting this right have stopped treating identity verification as a formality and started treating it as a real security control.
In practice, that means moving away from knowledge-based authentication toward something that actually confirms who a person is, not just what they know. For helpdesks, that looks like a real-time identity check before any account change is processed: a quick verification via government ID and a selfie, confirming that the person making the request is the legitimate account holder. It adds seconds to the interaction and closes a gap that can otherwise be exploited indefinitely.
For onboarding, it means verifying the person creating the account before the account is created, and establishing an identity anchor at enrollment that can be used for reverification throughout the student's time at the institution.
The technology to do this is available. The harder shift is recognizing that verification processes designed years ago were built for a different threat environment. Adjusting them isn't a luxury.
The Takeaway
Every breach in the higher ed sector adds to a growing pool of student and faculty data that's available to anyone willing to look for it. Names, email addresses, student IDs, dates of birth: this information is out there, and more surfaces with every incident.
That changes what identity verification needs to be. Asking for information that an attacker plausibly already has is no longer a meaningful check. It's an open door.
Higher education institutions owe it to their students to take a hard look at how they're handling identity at the moments that matter most: account creation, password recovery, helpdesk support. The breach that put student data at risk may not even be one the institution experienced directly. The responsibility for what happens next still lands with them.
Nametag helps universities verify student and faculty identity at the helpdesk, during onboarding, and throughout the account lifecycle, without storing biometric data and without slowing anyone down. Learn more at getnametag.com.