Self-service password reset (SSPR) can eliminate half of your helpdesk tickets and save substantial time for your users. But it can also create major security vulnerabilities unless implemented properly. This article explores how SSPR works, including the pitfalls of SSPR and how to avoid them.
What is Self-Service Password Reset (SSPR)?
Self-service password reset (SSPR) is a function that allows people to reset their own passwords for their online accounts. Instead of having to contact IT or customer support to reset their password for them, SSPR lets user do it on their own. SSPR functions are typically baked into an IAM platform or enterprise application, or offered via a third-party service.
How SSPR Works
Self-service password reset works by giving users a workflow through which they can reset their own password. In the enterprise, SSPR is most relevant in the context of Identity & Access Management (IAM), wherein a single identity provider is used to access multiple online accounts. Identity providers typically include an SSPR function as a feature within their platforms, but embedded SSPR typically has security and user experience drawbacks as explained below.

Standard SSPR workflow:
- Initiate reset
- Verify identity
- Reset password
SSPR workflows can be fast and simple or more complex, depending on the systems involved and level of security required. Generally speaking, a more complex SSPR flow is usually more secure. However, as we explain further down, not all security factors are equally secure.
How to Enable SSPR
Most major identity providers (Okta, Microsoft Entra, Cisco Duo, etc.) offer some form of self-service password reset capability. In all cases, a system administrator must set up the SSPR workflows using their admin console.
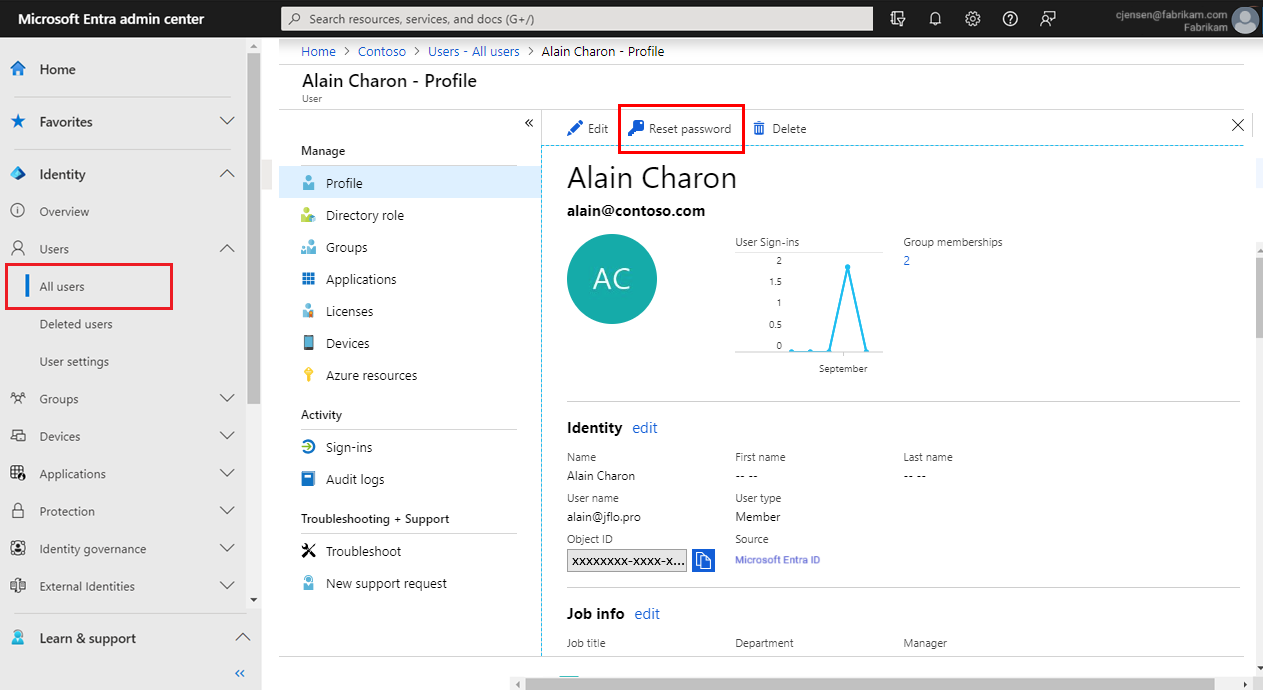
Different IAM platforms offer a choice of authentication factors to protect the password reset process. Okta, for example, offers "Reset Via Email" and "Reset via SMS" as default options. Microsoft Entra's default options are mobile app notifications/mobile app codes, email verification, and mobile phone verification.
It's worth noting, however, that all of these verification factors are vulnerable to interception or man-in-the-middle attacks, and can be extremely frustrating for users due to their inflexibility.
Learn more:
Pitfalls to Avoid with Self-Service Password Reset (SSPR)
Enabling self-service password resets can be a good way to ease the burden on overwhelmed IT and support teams. But SSPR can actually undermine your security posture if not implemented properly.
When someone tries to reset a password, the system first needs to verify that the user is legitimate. Hackers frequently exploit account recovery procedures for account takeovers, so this step is critical. But most of the SSPR verification methods offered by IAM providers are extremely vulnerable to common cyberattacks. They can also be very frustrating, leading users to contact support for help anyway.
This is also why identity and access management (IAM) tools like Okta and Microsoft Entra do not offer self-service MFA resets. Simply put, the verification factors used by traditional SSPR platforms are not secure enough to be used in such an extremely high-risk moment. As a result, users are forced to contact the IT helpdesk to reset their MFA manually.
Insecure Security Questions
Security questions are one of the most common verification methods used by most SSPR products. But the answers to these questions are often static and can be easily guessed or found through social engineering or public information. For instance, common questions about one's childhood pets, address, or parent’s name are frequently available on social media.
Security questions are so insecure that most organizations have spent years moving away from them, especially for high-risk actions like account recoveries. But SSPR systems often rely on security questions, despite their known vulnerabilities and user experience problems.
One-Time Passcode (OTP) Interception
Passcodes sent via text message or email are frequently used for authentication during self-service password reset. However, attackers have numerous tactics and tools at their disposal to intercept OTPs. In act, most security professionals now recommend moving away from OTPs entirely.
- SMS interception: Attackers can intercept text messages through techniques like SIM swapping or via an MFA bypass kit. Sometime text messages never arrive, forcing users to contact your support team.
- Email interception: Personal email accounts are often only protected by a password. If an attacker can compromise a person’s email, they can retrieve a passcode sent to that email.
Unreliable Authenticator Apps
While authenticator applications like Microsoft Authenticator offer a more secure alternative to SMS or email OTPs, they have major drawbacks that must be taken into account. Self-service password reset systems that rely on authenticator apps for user verification create security risks, and frustrated users may end up having to contact support anyway.
- Push fatigue attacks: Attackers bombard users with authentication prompts, often at awkward times like the middle of the night. Confused, frustrated users hit “accept” just to stop being spammed.
- Device changes: Users who lose their device, upgrade their phone, or delete their authenticator app can find themselves unable to access the push notification required for account recovery.
Secure SSPR with Nametag
Nametag offers a complete solution for self-service password reset (SSPR) that is far more secure, and works across your IAM providers to eliminate up to 50% of your helpdesk tickets while stopping account takeovers.
First-time users verify in under 30 seconds using only their photo ID and a selfie. Returning users benefit from selfie-only express reverification, and a seamless transition between devices if they lose or upgrade their phone.
Watch a demo of self-service password resets with Nametag
Plug-and-play integrations with Okta, Microsoft Entra, Cisco Duo, and other identity providers deploy in minutes with zero development work required. The entire solution can get up and running in under 10 minutes, immediately deflecting password reset tickets to self-service while protecting user accounts against impersonation attempts and takeover.
Explore our integrations
Behind the scenes, workforce-grade Deepfake Defense™ identity verification leverages a unique combination of cryptography, biometrics and AI to verify legitimate users in seconds while stopping advanced impersonation attacks that beat other authentication factors and identity verification tools.
Learn more about Deepfake Defense™
Explore our SSPR solution, then contact us for a live demo or more info!